
Top Solutions for HIPAA Compliant Network Security
Why Healthcare Network Security Solutions Are Critical Right Now
Healthcare network security solutions are the tools, frameworks, and strategies that protect patient data, medical devices, and clinical systems from cyberattacks — while keeping care delivery running without interruption.
Here are the most effective solutions used in healthcare today:
Solution What It Does Zero Trust / Microsegmentation Stops attackers from moving laterally across your network Next-Gen Firewalls (NGFW) Filters traffic and blocks threats at the perimeter Endpoint Protection Secures workstations, laptops, and legacy medical devices IoMT Security Platforms Monitors and isolates connected medical devices SIEM / Deep Observability Detects threats faster using network-wide intelligence SOC as a Service Provides 24/7 monitoring without in-house staffing VPN Encryption Protects remote access to clinical systems HIPAA-Aligned Access Controls Limits who can access protected health information (PHI)
Healthcare is one of the most targeted industries for cyberattacks — and the stakes couldn't be higher. A breach doesn't just cost money. It can delay surgery, expose patient records, and destroy the trust patients place in their providers.
The numbers back this up. The average healthcare data breach costs $7.42 million — more than $3 million above the global average across all industries. Ransomware attacks against healthcare organizations jumped 328% in just the first half of 2022 alone.
At the same time, healthcare networks are getting more complex. Electronic health records (EHRs), cloud systems, telemedicine platforms, and thousands of connected medical devices have expanded the attack surface dramatically. Legacy systems that were never designed with security in mind are still running in many hospitals today.
The result? Security teams are stretched thin, compliance requirements like HIPAA are tightening, and the cost of doing nothing keeps rising.
I'm Michael Gaigelas II, and I've spent my career helping organizations in regulated industries implement practical, cost-effective healthcare network security solutions — including rapid HIPAA compliance, Zero Trust architecture, and endpoint protection built for complex clinical environments. In the sections below, I'll walk you through the top solutions, frameworks, and strategies you need to protect your network and stay compliant.

Primary Cybersecurity Challenges in Modern Healthcare
The modern healthcare environment is a bit like a digital frontier. We are seeing a massive shift toward digital transformation, but this progress comes with significant growing pains. One of the biggest hurdles we face is the global shortage of cybersecurity professionals. It is estimated that there are millions of unfilled positions in the field, making it difficult for hospitals to find the talent they need to man the digital walls.
Interestingly, while the talent gap is real, healthcare organizations that have dedicated information security staff are becoming more common. Research shows that about 60% of organizations now have a dedicated CISO, and 80% have dedicated security staff. This is a huge improvement from just a few years ago, but it’s still not enough to combat the sheer volume of threats.
Beyond staffing, healthcare providers must navigate:
Legacy Systems: Many clinical environments rely on older hardware and software that can't be easily patched, creating "sitting duck" vulnerabilities.
Remote Service Adoption: While telehealth lowers costs and increases access, it expands the network perimeter to include unmanaged home networks.
Service Continuity: Unlike a retail shop, a hospital cannot afford "down time." If the network goes down, patient lives are literally on the line.
Internal Risks: It’s a tough pill to swallow, but intentional attacks by internal employees are often ten times as costly as external ones.
To stay ahead, organizations need robust cybersecurity services that account for these human and technical variables. Furthermore, scientific research on medical device development and analytics is constantly pushing the boundaries of what these devices can do, which in turn requires our security solutions to be just as innovative.
The Impact of Ransomware and Internal Risks
Ransomware isn't just a "virus" anymore; it’s a business-stopping disaster. When an attacker gains entry, they look for "lateral movement"—the ability to hop from a receptionist's computer to the server holding the Electronic Health Records (EHR).
With the average breach cost sitting at $7.42 million, the financial impact is devastating. But we also have to look inward. Employee errors—like clicking a phishing link or misconfiguring a database—account for a massive portion of data exposures. Whether it’s an accidental mistake or an intentional disruption, internal risks require constant monitoring and strict access controls.
Securing the IoMT: Healthcare Network Security Solutions for Connected Devices
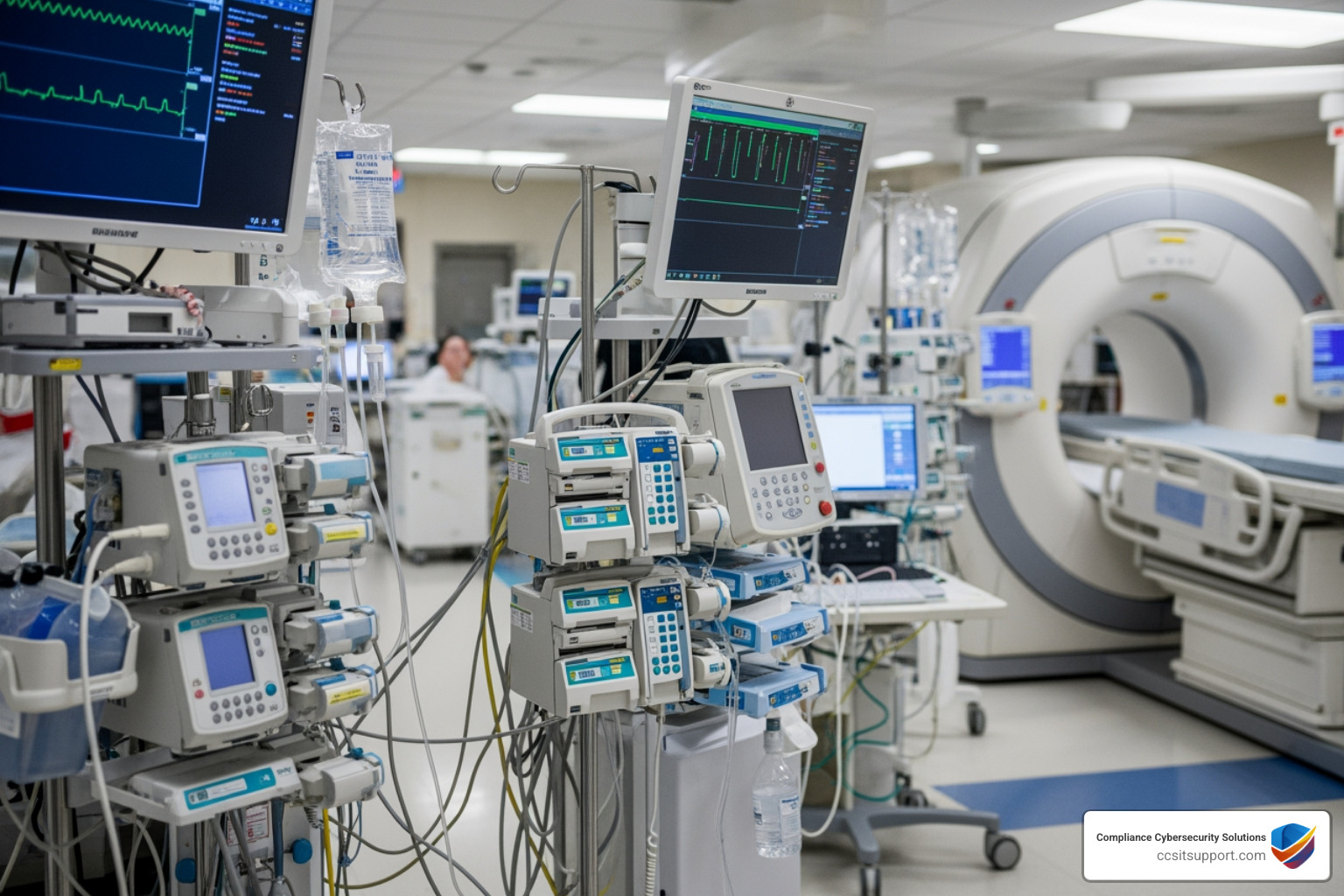
The Internet of Medical Things (IoMT) is a double-edged sword. On one hand, having an infusion pump or an MRI machine connected to the network allows for real-time data sharing and better patient outcomes. On the other hand, many of these devices were built for function, not security. They often lack the ability to run traditional antivirus software.
To secure these assets, we need healthcare network security solutions that provide deep visibility. You can't protect what you can't see. Modern platforms can now identify every device on the network, from a surgeon's tablet to a smart heart monitor, and categorize them by risk level.
Our support center services often encounter situations where a single unpatched device acts as the entry point for a network-wide infection. Real-time monitoring and asset identification are the first steps in ensuring that these critical care devices don't become liabilities.
Strategies for Medical Device Protection
Protecting medical devices requires a specialized approach. Since we often can't install software directly on the device, we have to protect the "pipes" they communicate through.
API Encryption: Ensuring that any data sent to or from a device is encrypted so it can't be intercepted.
Real-Time Telemetry: Monitoring the behavior of devices. If a heart monitor suddenly starts trying to access the payroll server, that’s a red flag.
Remote Monitoring: Using cloud-based platforms to keep an eye on device health and security status 24/7.
Patch Management: While difficult, keeping firmware updated is essential for closing known security holes.
By maintaining high operational uptime and using dedicated medical device security platforms, providers can ensure that the "mission-critical" remains "mission-secure."
Implementing Zero Trust and Microsegmentation
The old way of securing a network was like a castle: a big moat (firewall) and a single gate. Once you were inside, you could go anywhere. In the "Post-Breach Era," we assume the attacker is already inside. This is where Zero Trust and microsegmentation come in.
Feature Traditional Perimeter Security Zero Trust Architecture Access Logic "Trust but verify" (inside is safe) "Never trust, always verify" Movement Easy lateral movement Movement restricted by policy Visibility Limited to the "gate" Deep observability across all segments Response Block at the edge Contain at the source (limit blast radius)
Zero Trust limits the "blast radius" of an attack. If a single workstation is compromised, microsegmentation ensures the attacker is stuck in a tiny digital room with nowhere else to go. This is achieved through identity-based security and dependency mapping—understanding exactly which systems need to talk to each other and blocking all other paths.
Advanced Healthcare Network Security Solutions for Lateral Movement
Microsegmentation is the "secret sauce" for modern healthcare network security solutions. By adjusting policies in real-time, we can stop an infection from spreading to the rest of the hospital. This provides a level of resilience that traditional firewalls just can't match.
For organizations using hybrid cloud environments, achieving this visibility is even more critical. You need to see traffic moving between your on-premise servers and your cloud-based EHR to ensure no unauthorized data is leaking out.
A Defense-in-Depth Framework for HIPAA Compliance
No single tool can do it all. We recommend a "defense-in-depth" approach, which is like having a fence, a burglar alarm, a security guard, and a safe.
This layered security includes:
Next-Generation Firewalls (NGFW): These do more than just block ports; they inspect the actual data packets for signs of malware.
IPS/IDS: Intrusion Prevention and Detection systems that act as a digital tripwire.
VPN Encryption: Essential for protecting PHI when doctors or staff work from home or satellite clinics.
Endpoint Protection: AI-powered software on every laptop and server that can "roll back" a ransomware attack with one click.
Regular risk assessments are the heartbeat of this framework. By following a "Security Wheel" process—constantly assessing, implementing, and monitoring—we can stay ahead of evolving threats. Our compliance services help Florida healthcare providers navigate these layers to ensure they meet federal standards without drowning in complexity.
Aligning Healthcare Network Security Solutions with HIPAA and HHS 405(d)
Compliance isn't just about checking a box; it’s about protecting patients. HIPAA mandates the privacy of Protected Health Information (PHI), but newer frameworks like HHS 405(d) provide more specific "best practices" for the healthcare sector.
Key requirements often include:
Audit Logging: Knowing exactly who accessed what data and when.
Access Controls: Ensuring only authorized personnel can see sensitive records.
Business Associate Agreements (BAA): Ensuring your vendors (like us!) are also held to high security standards.
NIS2 Directive Alignment: For organizations with international ties, preparing for stricter standards like NIS2 (effective late 2024) is becoming a priority.
Managed Services and Cyber-Physical Integration
For many healthcare providers in Florida, running a 24/7 Security Operations Center (SOC) is too expensive. This is where managed services like SOC as a Service and NOC support come in. We provide the "eyes on glass" 24/7/365, so you don't have to.
We are also seeing a trend called cyber-physical convergence. This means integrating your digital security with your physical security. Imagine a single management console where you can monitor your network traffic, your hospital's surveillance cameras, and even facial recognition or weapons detection systems. This unified approach optimizes management and ensures that a physical breach doesn't lead to a digital one.
Developing a Comprehensive Security Policy
Before you buy a single piece of software, you need a plan. A formal security policy defines:
Roles and Responsibilities: Who is in charge during an emergency?
Acceptable Use: What can employees do (and not do) on the network?
Risk Matrix: A way to calculate the impact of different threats (e.g., Threat x Vulnerability).
Staff Training: Teaching nurses and doctors how to spot a suspicious email is often the most effective security tool you have.
Modular blueprints allow us to scale security for different site sizes—from a small 5-person practice to a large hospital system with over 500 users.
Frequently Asked Questions about Healthcare Security
How does microsegmentation prevent ransomware spread in hospitals?
Microsegmentation divides the network into small, isolated zones. If ransomware hits a computer in the billing department, the security policy prevents that computer from communicating with the clinical servers or medical devices. This "digital quarantine" stops the attack in its tracks.
What are the primary regulatory requirements for healthcare networks?
The big one is HIPAA (Health Insurance Portability and Accountability Act), which focuses on the privacy and security of PHI. Additionally, the HHS 405(d) "Health Industry Cybersecurity Practices" (HICP) provides a roadmap for managing the top five cybersecurity threats in the industry.
Why is the cost of a healthcare data breach higher than other industries?
Healthcare breaches are more expensive because the data is "high-value" and permanent. You can change a credit card number, but you can't change your medical history or Social Security number. Additionally, the regulatory fines, the cost of specialized forensic investigations, and the potential for clinical disruption add significant weight to the final bill.
Conclusion
The path to digital sovereignty in healthcare is paved with proactive defense and scalable operations. By implementing healthcare network security solutions that focus on Zero Trust, IoMT visibility, and a layered defense-in-depth strategy, you can protect your practice and your patients from the ever-growing threat landscape.
At Compliance Cybersecurity Solutions (CCS), we specialize in aligning your IT infrastructure with the rigorous demands of HIPAA and other regulated standards. Whether you are looking for managed SOC services or a complete network overhaul, we are here to help Florida's healthcare providers stay secure and compliant.
For top-tier HIPAA compliance and network security, reach out to our team today. Let’s build a network that supports your mission of care without compromising on security.

