
The Essential Guide to Healthcare Cybersecurity HIPAA Compliance
Why Healthcare Cybersecurity HIPAA Compliance Can No Longer Wait
Healthcare cybersecurity HIPAA compliance is the practice of protecting patients' electronic health information (ePHI) by following the security standards set by the Health Insurance Portability and Accountability Act — and right now, it has never been more urgent.
Here's what you need to know at a glance:
What Why It Matters HIPAA Security Rule Requires administrative, physical, and technical safeguards for all ePHI Who must comply Health plans, providers, clearinghouses, and their business associates Biggest threats Ransomware, phishing, social engineering, third-party breaches Cost of failure Average healthcare breach cost $9.77 million in 2024 Enforcement HHS Office for Civil Rights (OCR) issues civil penalties; DOJ handles criminal cases
The numbers are hard to ignore. Healthcare was the most breached industry in 2024. Over 90% of U.S. healthcare organizations experienced a cyberattack in the past year. Ransomware groups claimed 13% more healthcare victims in 2024 compared to the year before. And 72% of healthcare organizations reported that cyberattacks directly disrupted patient care.
This isn't just a compliance checkbox problem. It's a patient safety problem.
The HIPAA Security Rule was built to give healthcare organizations a flexible, scalable framework to defend against exactly these kinds of threats — but only if it's implemented correctly. Many organizations still have dangerous gaps: outdated risk assessments, undertrained staff, poorly managed vendors, and no tested incident response plan.
This guide walks you through everything you need to know — from the core requirements of the HIPAA Security Rule to real-world breach lessons, risk analysis, cloud vendor management, and breach response.
I'm Michael Gaigelas II, and I've spent my career helping healthcare and other regulated-industry organizations achieve rapid, cost-effective HIPAA and cybersecurity compliance — closing security gaps before they become million-dollar breaches. My hands-on work in healthcare cybersecurity HIPAA compliance gives me a practical perspective on what actually works for organizations with limited IT resources and real regulatory pressure.
Understanding the HIPAA Security Rule and ePHI Protection
When we talk about healthcare cybersecurity HIPAA requirements, we are primarily looking at the Security Rule. While the Privacy Rule protects all forms of Protected Health Information (PHI)—whether it’s spoken, on paper, or digital—the Security Rule is the technical "muscle." It specifically focuses on Electronic Protected Health Information (ePHI) that is created, received, maintained, or transmitted by a regulated entity.
The Security Rule isn't just a list of "don'ts." It's a set of national standards designed to ensure the confidentiality, integrity, and availability of patient data. To stay on the right side of the law, organizations must implement three types of safeguards: Administrative, Physical, and Technical.
One of the most important things to remember is that HIPAA is "technology-neutral" and "scalable." This means the rules for a massive hospital chain in Miami look different from those for a small private practice in Fort Lauderdale. The law allows us to choose security measures that are appropriate for our size, resources, and the complexity of our operations.
If you want to dive deep into the legal jargon, you can check out the eCFR.gov Regulatory API for the full text of the law. However, most of our clients prefer a more hands-on approach. At CCS, we specialize in translating these complex regulations into compliance services that actually protect your business without making your daily operations a nightmare.
Who Must Comply: Covered Entities and Business Associates
Not everyone who touches health data is subject to HIPAA, but the net is wider than you might think. Generally, there are two main groups:
Covered Entities: This includes health plans (like HMOs and Medicare), healthcare clearinghouses, and healthcare providers who conduct certain financial and administrative transactions electronically.
Business Associates: These are the vendors and service providers that handle ePHI on behalf of a covered entity. This includes IT providers like us, cloud storage companies, lawyers, and billing services.
If you aren't sure where you fall, the CMS Covered Entity Decision Tool is a great place to start.
The biggest shift in recent years came from the HITECH Act, which made Business Associates (BAs) directly liable for HIPAA Security Rule violations. This means if your cloud provider loses patient data because they didn't have proper encryption, the Office for Civil Rights (OCR) can come after them directly. It also means that having a signed Business Associate Agreement (BAA) is not just a suggestion—it's a legal necessity.
The Core Safeguards of Healthcare Cybersecurity HIPAA
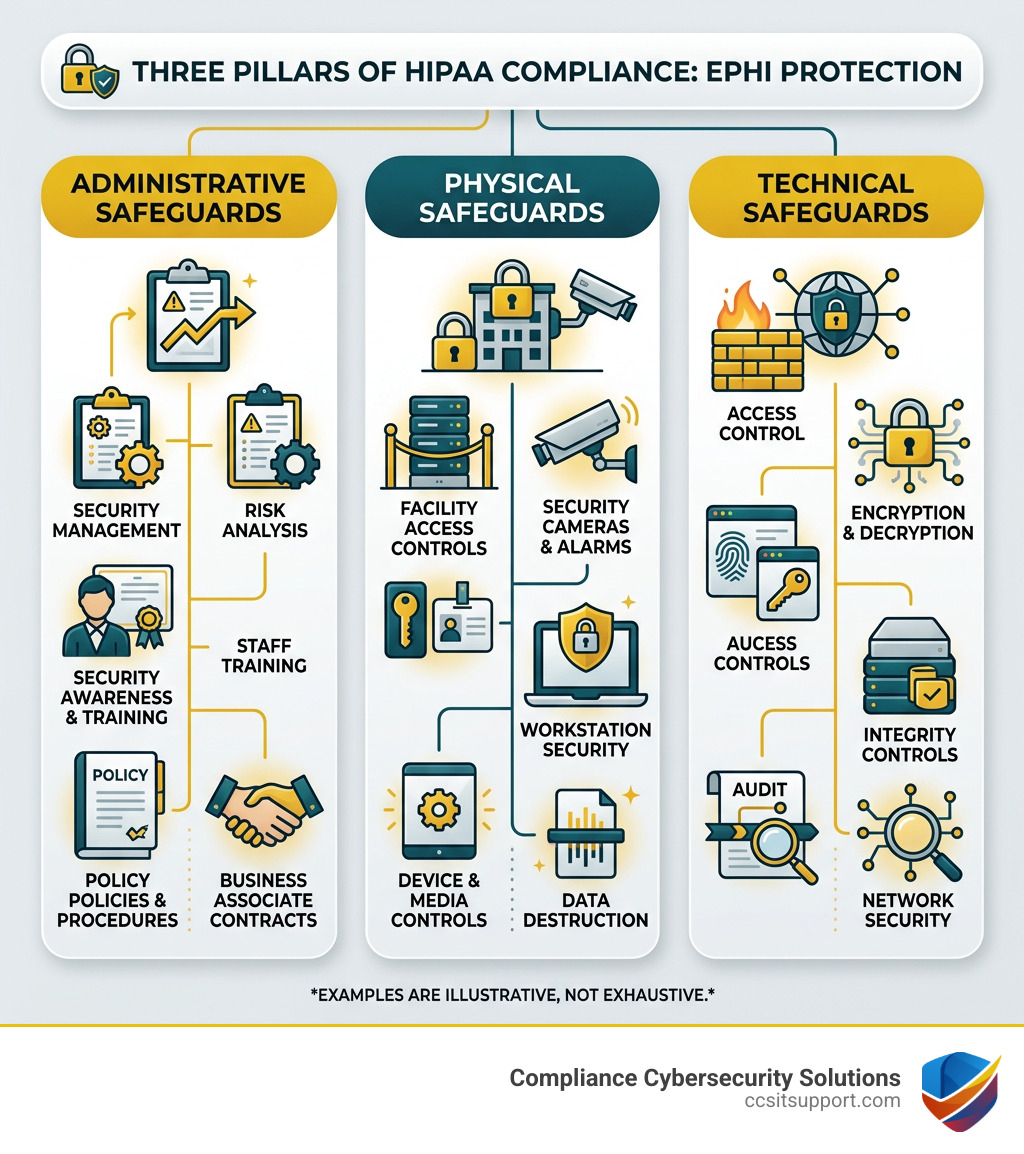
To achieve healthcare cybersecurity HIPAA compliance, we have to look at the three pillars of the Security Rule:
Administrative Safeguards: These are the "brains" of your security program. They include things like performing a risk analysis, designating a security official, and managing workforce training. Think of this as the paperwork and planning that makes the technical stuff work.
Physical Safeguards: You can have the best firewall in the world, but it won't matter if someone can walk into your office and steal a server. These safeguards cover facility access controls, workstation security, and how you dispose of old hardware.
Technical Safeguards: This is the "high-tech" side of the house. It includes access controls (making sure only the right people see the data), audit logs (tracking who looked at what), and data encryption.
For a deeper dive into the technical side, the HHS Technical Safeguards Guidance provides a roadmap for what "reasonable and appropriate" protection looks like in a modern digital environment.
Navigating the Modern Threat Landscape in Healthcare
The healthcare industry is currently under siege. In 2024, the average cost of a healthcare data breach skyrocketed to $9.77 million. Why is it so expensive? Because it’s not just about the data; it’s about the downtime. When a hospital's systems go dark, surgeries are canceled, and patients have to be diverted to other facilities.

Lessons from High-Profile Data Breaches
Recent years have given us some painful examples of what happens when healthcare cybersecurity HIPAA measures fail. The Change Healthcare breach in early 2024 was a watershed moment. It disrupted claims processing across the entire country, leaving many providers unable to get paid for weeks.
Before that, the Anthem breach affected nearly 80 million individuals, leading to record-breaking fines and massive reputational damage. These incidents show that even the biggest players are vulnerable if their defenses aren't layered and proactive.
Mitigating Risks with Healthcare Cybersecurity HIPAA Strategies
So, how do we fight back? It starts with understanding the specific threats we face.
Threat How it Works HIPAA Mitigation Ransomware Encrypts your data and demands a fee for the key. Frequent backups and a tested Contingency Plan. Phishing Deceptive emails designed to steal login credentials. Ongoing Security Awareness Training for all staff. Social Engineering Manipulating employees into giving up sensitive info. Strict Access Control and authentication policies. IoMT Vulnerabilities Exploiting unpatched medical devices (pumps, monitors). Regular vulnerability scanning and network segmentation.
One of the most effective ways to align your defenses is by using the NIST to HIPAA Security Rule Crosswalk. This document helps us map the high-level NIST Cybersecurity Framework to the specific regulatory requirements of HIPAA, giving you a more robust security posture. If you're feeling overwhelmed by the technicalities, our cybersecurity services are designed to take the weight off your shoulders.
Foundational Requirements: Risk Analysis and Management
If HIPAA were a house, the Risk Analysis would be the foundation. You cannot protect what you haven't identified. The Security Rule requires all covered entities and business associates to conduct an "accurate and thorough" assessment of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of ePHI.
This isn't a "one and done" task. We recommend performing a risk analysis at least once a year, or whenever you make a major change to your IT environment (like moving to a new cloud provider or opening a new office in Florida).
To help smaller practices, the government provides the HHS Security Risk Assessment Tool. While this tool is helpful, it’s just a starting point. A true risk management strategy involves taking the findings from that assessment and actually fixing the holes.
Shared Responsibility in Cloud and Third-Party Vendor Management
Many healthcare providers assume that if they use a major cloud provider, they are automatically HIPAA compliant. We hate to be the bearers of bad news, but that’s not how it works.
Compliance in the cloud follows a "Shared Responsibility Model." The cloud provider is responsible for the security of the cloud (the physical servers and data centers), but you are responsible for security in the cloud (how you configure access, who has passwords, and whether the data is encrypted).
This is why HHS Business Associate Guidance is so critical. You must have a BAA in place with every vendor that touches your data. This agreement outlines exactly how they will protect your ePHI and what happens if they have a breach.
Incident Response and the Breach Notification Rule
Even with the best healthcare cybersecurity HIPAA strategy, things can go wrong. When they do, the clock starts ticking. The HIPAA Breach Notification Rule requires us to notify affected individuals, the Secretary of HHS, and, in some cases, the media.
If a breach affects 500 or more individuals, you must notify the OCR "without unreasonable delay" and no later than 60 days after discovery. If it’s fewer than 500 people, you can keep a log and report it annually.
Knowing what to do in those first few hours can save your organization millions. We highly recommend watching the HHS Video: Responding to Cyber-Related Security Incidents to understand the government's expectations for incident response.
Healthcare Cybersecurity HIPAA Compliance Best Practices
After years of helping organizations in Florida navigate these waters, we've identified a few "must-haves" for any modern healthcare security program:
Security Awareness Training: Your employees are your first line of defense—or your weakest link. Regular training on how to spot a phishing email is the single best investment you can make.
Multi-Factor Authentication (MFA): If you aren't using MFA for every single login that touches ePHI, you are leaving the front door wide open.
Encryption Everywhere: Encrypt data at rest (on your servers/laptops) and in transit (emails and uploads). If encrypted data is stolen, it’s often not considered a "reportable breach" under the HIPAA safe harbor rules.
Stay Informed: Sign up for the OCR Cyber Awareness Newsletters to stay ahead of new threats and regulatory changes.
Frequently Asked Questions about Healthcare HIPAA Security
What are the potential penalties for HIPAA cybersecurity violations?
The penalties for non-compliance are no joke. They are categorized into four tiers based on the level of "culpability":
Tier 1 (No Knowledge): $137 to $34,464 per violation.
Tier 2 (Reasonable Cause): $1,379 to $68,928 per violation.
Tier 3 (Willful Neglect - Corrected): $13,785 to $68,928 per violation.
Tier 4 (Willful Neglect - Not Corrected): $68,928 to $2,067,813 per violation.
Beyond the fines, the OCR often requires a Corrective Action Plan (CAP), which can involve years of intrusive government monitoring. In extreme cases, the Department of Justice (DOJ) can even pursue criminal charges for the "knowingly" wrongful disclosure of PHI.
How does the NIST Cybersecurity Framework map to HIPAA?
The NIST Cybersecurity Framework (CSF) is a voluntary set of standards that many organizations use to build a robust security program. While HIPAA tells you what you must protect, NIST provides a more detailed "how-to" guide. By mapping NIST controls to HIPAA requirements, we can ensure that we aren't just checking a compliance box, but actually building a resilient system that can withstand modern attacks.
Is a Business Associate Agreement enough for cloud security?
Absolutely not. A BAA is a legal contract, not a technical configuration. You can have the most perfectly drafted BAA in the world, but if your staff is using "Password123" to access a cloud database, you are still in violation of HIPAA. You must ensure that your technical settings—like encryption, access logs, and session timeouts—are correctly configured within the cloud environment.
Conclusion
Achieving healthcare cybersecurity HIPAA compliance doesn't have to be a source of constant stress. By breaking the requirements down into manageable pieces—starting with a solid risk analysis and moving into layered technical safeguards—you can protect both your patients and your business.
At CCS Compliance & Cybersecurity Solutions, we live and breathe this stuff. Based right here in Florida, we understand the local landscape and the specific pressures healthcare providers face. Whether you need help developing policies, implementing threat detection, or training your team, we're here to help you align your IT with the highest regulatory standards.
Don't wait for a $9 million wake-up call. Protect your organization with expert healthcare cybersecurity today and get back to what you do best: caring for your patients.

